Ethiopia Introduces Deep Packet Inspection

The Ethiopian Telecommunication Corporation, which happens to be the sole telecommunication service provider in Ethiopia, has deployed or begun testing Deep Packet Inspection (DPI) of all Internet traffic. We have previously analyzed the same kind of censorship in China, Iran, and Kazakhstan.
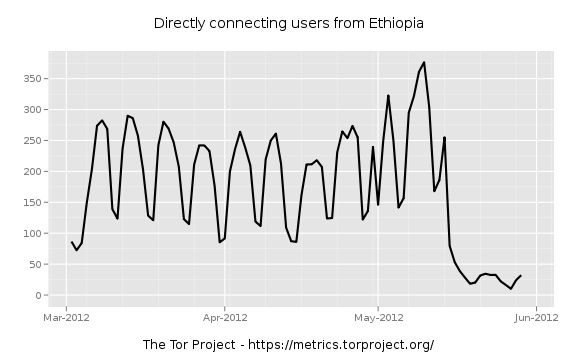
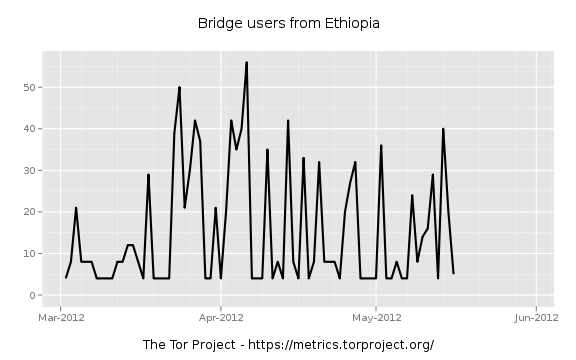
Reports show that Tor stopped working a week ago -- even with bridges configured. Websites such as https://gmail.com/, https://facebook.com/, https://twitter.com/, and even https://torproject.org/ continue to work. The graphs below show the effects of this deployment of censorship based on Deep Packet Inspection:
An analysis of data collected by a volunteer shows that they are doing some sort of TLS fingerprinting. The TLS server hello, which is sent by the Tor bridge after the TLS client hello, never reaches the client. We don't know exactly what they are fingerprinting on, but our guess is that it is either the client hello or the server hello. An illustration can be found in this network flow diagram.
Thanks to Philipp Winter and George Kadianakis for helping me analyze the data. If you have more information about the censorship in Ethiopia, please email help@rt.torproject.org.
Comments
Please note that the comment area below has been archived.
On the Democracy Index
On the Democracy Index Ethiopia ranks low at 121 of 167
right between Morocco and Kuwait. It is considered as an
authoritarian regime. No surprise here.
I remember they deal a lot with China which is always eager to
include its telecom technologies in their deals.
Thank you guys for exposing
Thank you guys for exposing the censorship in Ethiopia from technical perspective. The Ethiopian Government has been applying a filtering/ blocking system from its only server/ Ethiopian Telecommunication/ to blog pro- democracy sites. People have used proxy servers to access block sites.
The government has also officially confirmed using air jamming technologies to jam radio transmission signals from VOA & pro democracy site; ESAT.
Guess now it's a leap forward to them! What a dictatorship!
I tried to browse internet
I tried to browse internet through tor in vain. For almost a week or two, it is difficult to access through Tor.
I thought the failure was due to slow internet connection. I now understand it is censorship. Melese Zenawi is a dictator, He is a killer. We need freedom, freedom, freedom.........
There's a way around it,
There's a way around it, please email help@rt.torproject.org for support.
This shows the level of
This shows the level of democracy in Ethiopia. We are preceded by Iran, China....This also shows the level of dictatorship of Melese Zenawi's empire in Ethiopia behind the curtain.
Back in the 1990s, they had
Back in the 1990s, they had that for voice telephones as well. A friend of mine was doing development work over there, and the phone company told him he wasn't allowed to speak Dutch on the phone, only local languages, Italian, and English, because they didn't have Dutch-speaking wiretappers.
Ethiopian government would
Ethiopian government would rather surveil its citizens than feed them.
Guess Chinese just sold one
Guess Chinese just sold one of DPI server to them.
Maybe, but we won't know
Maybe, but we won't know unless we figure out what they are fingerprinting us on.
Any advise on what to do to
Any advise on what to do to maintian ananimity and security? Apriciate your continued work and it is saving lives from tyrants.
There is a way to get around
There is a way to get around this and still use Tor. Please email help@rt.torproject.org for support.
This needs to be fixed ASAP,
This needs to be fixed ASAP, what if China & Iran start blocking TOR using this method, you need to get an update out fast.
We are working on updating
We are working on updating the Obfsproxy Tor Browser Bundles (see https://www.torproject.org/projects/obfsproxy.html.en for details on Obfsproxy).
any advise on how to
any advise on how to overcome this?
We are working on updated
We are working on updated Obfsproxy Tor Browser Bundles, which will enable users to circumvent this censorship. In the meantime, you can use one of the private bridges we have set up. Please email help@rt.torproject.org for details.
I get the following
I get the following warning
Jun 02 16:27:19.651 [Warning] You have a Bridge line using the bridge pluggable transport, but there doesn't seem to be a corresponding ClientTransportPlugin line.
Jun 02 16:27:20.651 [Notice] Bridge at '38.229.33.18:42401' isn't reachable by our firewall policy. Skipping.
.............................
what can i do?
Where do you get that? Is
Where do you get that? Is this from a Tor bundle, or from a standalone tor installation?
Check your torrc for any lines like 'Bridge bridge ' instead of 'Bridge '.
You can e-mail
You can e-mail help@rt.torproject.org to get a working bridge.
How can you show statistics
How can you show statistics over the number of Tor users in Ethiopia? Isn't Tor supposed to be anonymous? Oh I guess you collect "not personally identifying" information such as country, IP address, time and date of connection..
See the paper called
See the paper called "Privacy-preserving Ways to Estimate the Number of Tor Users": https://metrics.torproject.org/papers/countingusers-2010-11-30.pdf
Is it safe to disable
Is it safe to disable NoScript if you have JavaScript disabled anyway?
Is it safe to disable HTTPS everywhere if you only go to https: websites all-ready?
Actually, NoScript is there
Actually, NoScript is there because it has some extra ways to prevent plugins from running. Its goal in TBB has nothing to do with blocking javascript. If you don't have any plugins anywhere on your hard drive (and you're really totally sure about that), disabling Noscript should be ok.
Disabling https everywhere should be fine too, if you know what you're doing. Oh, and also if you never visit any websites that link to anything other than https links.
They fear that an incident
They fear that an incident like Arab uprising may happen through facebook. Anyways, can't stop people power by doing so. As we have seen recently, 21st century has no good for Dictators.
Your decision to make the
Your decision to make the Tor Button always enabled was cruel. I just lost all my tabs! :( Think of all customers next time!
This is Very Sad. I was a
This is Very Sad. I was a fan of tor When I was in Ethiopia. The government is building ( built) a huge firewalls to suppress the freedom of Ethiopian people.
Guys and gals, I know you
Guys and gals, I know you are all concerned about the people of Ethiopia. Currently, we don't have any issue about security. We need to feed ourselves and you know get concerned about other issues later. So, don't get bothered. If you are talking about foreigners residing in Ethiopia, then go ahead and do your mission. Sure, it is food that the people of Ethiopia need now, not security concerns, though it will be in the future.
This is weyane strategies to
This is weyane strategies to confused the people of Ethiopia we know what to do thanks for you suggestion
Bypassing the censorship, is
Bypassing the censorship, is it, and instead. Look, they called them Bullo, just for gain. They were always censored in an ancient country that never knew any digital or electronic practice. They were used to plough and produce, from the harvest. Did they stop them from eating some while in bondage? On average, one bull consumes around 4Kg of the produce while working under bondage. The greed could not totally tie their mouth, because it was scared that it would loose them for the next year bold round of harvest and to suffocation. Practice it, like that and bypass it. Alas!
Regime trolls on the
Regime trolls on the internet are like government minders on the killing fields? Now that´s the peak of global civilisation...
It also appears that DPI in
It also appears that DPI in Ethiopia is also blocking OpenVPN VPN.
how do international
how do international companies conduct business if they are blocking VPN connections? I was planning to deploy a site-to-site IPSec VPN to connect two offices in Ethiopia and USA. I guess I should look in to that more.
Hi Friends, U can also
Hi Friends, U can also witness that they are expending our money collected from taxation to secure their power paying for resources just to oppress our freedom and right through censorship act . This is what happening in that poor country having less than 1% population who had access to Internet / web.sorry,sorry,sorry .