Obfsproxy: the next step in the censorship arms race

On Feb 9, Iran started to filter SSL connections on much of their network. Since the Tor protocol uses SSL, that means Tor stopped working too — even Tor with bridges, since bridges use SSL too.
We've been quietly developing Obfsproxy, a new tool to make it easier to change how Tor traffic looks on the network. In late 2011 Iran moved into the #2 position in global Tor user count, and several important political events are scheduled in Iran this month and next. This situation seemed like a good time to test our new tool while also helping improve Internet freedom around the world.
We started with a "Tor Obfsproxy Browser Bundle" with two test obfsproxy bridges in it, to verify that it worked in-country. Then we got over 300 volunteers running more obfsproxy bridges (even with our complex build instructions!), and picked fourteen fast stable trustworthy obfsproxy bridges for an updated bundle which we put out the morning of Feb 11. We spent the weekend fixing usability, stability, and scalability bugs, and put out another bundle on Feb 13 with new versions of Vidalia, Tor, and Obfsproxy.
Thousands of people in Iran successfully used the Obfsproxy Bundle over the weekend:
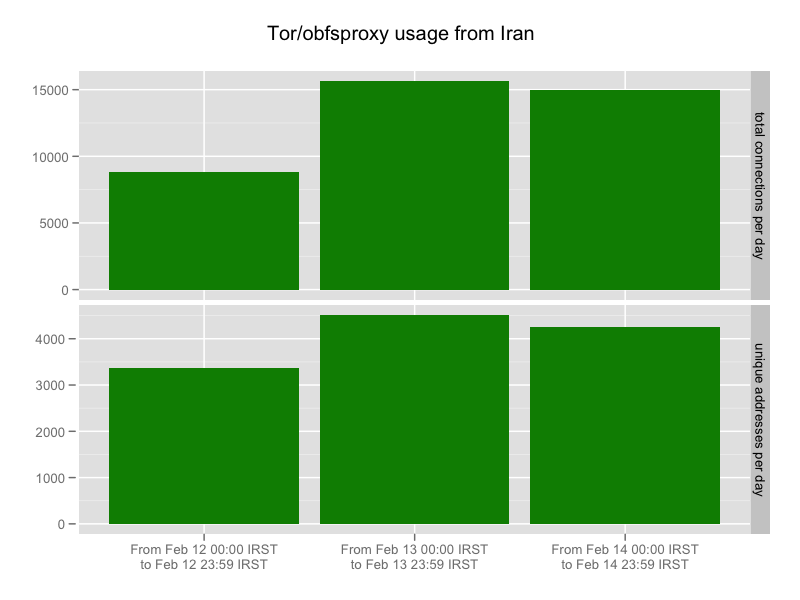
We did some spot-checking and it seems that the new addresses on Feb 14 are mostly different from the new addresses on Feb 13; but I would guess these are mostly returning users with dynamic IP addresses, rather than actually fresh users. More importantly, these people will be thinking about Obfsproxy next time the filter cracks down — and based on current events, that next time won't be far off. Finally, even though it looks like SSL and Tor are back, I expect Iran will keep throttling SSL traffic as they've been doing for months, so the Obfsproxy bundle will still be more fun to use in Iran than the normal Tor bundles.
How does it work?
Deep Packet Inspection (DPI) algorithms classify Internet traffic by protocol. That is, they look at a given traffic flow and decide whether it's http, ssl, bittorrent, vpn, etc. Governments like Iran, China, and Syria increasingly use these tools (and they often purchase them from Western corporations, but that's a different story) to implement their country-wide censorship, either by looking for a given protocol and outright blocking it, or by more subtle mechanisms like squeezing down the bandwidth available to a given protocol to discourage its use.
Obfsproxy's role is to make it easy for Tor's traffic flows to look like whatever we like. This way Tor can focus on security and anonymity, and Obfsproxy can focus on appearance. The first thing we decided to try looking like was nothing at all: the "obfs2" module adds an encryption wrapper around Tor's traffic, using a handshake that has no recognizable byte patterns.
It won't work perfectly. For example, the traffic flows will still have recognizable timing, volume, and packet size characteristics; a good entropy test would show that the handshake looks way more random than most handshakes; and the censors could always press the "only allow protocols my DPI box recognizes" panic button. Each step in this arms race aims to force the censor to a) put more development time and DPI resources into examining flows, and b) risk more false positives, that is, risk blocking innocent users that they didn't realize they'd be blocking.
This particular new obfuscating layer isn't the most important feature of Obfsproxy. The best part is that makes it easy to design, deploy, and test other obfuscating layers without messing with the rest of Tor. There's a lot of research into trying to make traffic flows look like other protocols, so for example we could rewrite the Tor flows as valid http that the DPI engine considers harmless. That problem is harder than it sounds — and it sounds hard. But by making a separate component that only has to worry about how the traffic looks, other researchers can try out different strategies without needing to learn so much about the rest of Tor. This approach will also let us easily plug in other transports like Telex, and it will also let other circumvention projects reuse Obfsproxy so they don't have to reinvent our wheels.
Moving forward
One of the choices we faced was how widely and loudly to mention the bundle. While we think it would be hard and/or risky for attackers to block the Obfsproxy protocol, the bundle included 14 preconfigured bridge addresses, and censors could just plug those addresses into their blacklists. We started the weekend telling people to only tell their close friends, but on Sunday we opted for a broader publicity push inside the activist community for two reasons. First, the new Vidalia release (0.2.17) lets users configure their own obfsproxy bridge addresses, so if the preconfigured addresses get blocked the user can just put in new ones. Second, it became clearer that the blocking would let up in a few days once the immediate political pressure was over, and we decided it was more important to get the word out about Obfsproxy in general so these users will know about it next time.
I should point out that I don't think they were targeting Tor here. They were targeting popular websites that use SSL, like Gmail and Facebook. Tor was collateral damage because we opted to make Tor traffic look like SSL. That said, we should not forget that we are on their radar: they targeted Tor by DPI in September 2011, and the Diginotar breakin obtained a fake SSL cert for torproject.org.
The next choice we face is: what other communities should we tell? The bundle works great in China too, where their aggressive censorship has been a real hassle for us the past year or so. Some other countries in Asia appear to be newly using DPI to recognize Tor traffic (more on that in an upcoming blog post). We have more development work to do before we can keep up with the China arms race, including teaching obfsproxy bridges to automatically report their addresses to us and teaching our bridgedb service to give them out, and we need to answer research questions around getting more bridges, giving them out in smarter ways, learning when they get blocked, and making it hard for censors to find them. We also need to spread the word carefully, since the arms race is as much about not drawing the attention of the censors as it is about the technology. But the Obfsproxy Bundle works out of the box right now in every censoring country we know of, so we shouldn't be too quiet about it.
And finally, thanks go to George Kadianakis for taking Obfsproxy on as his Google Summer of Code 2011 Project; to Nick Mathewson for mentoring him and getting the Obfsproxy architecture going in the right direction; to Sebastian Hahn for spending all weekend with me fixing bugs and making packages; and to Karsten Loesing, Erinn Clark, Robert Ransom, Runa Sandvik, Nick, George, and the broader Tor community for stepping up over the weekend to help us take it from "early prototype" to "deployed software in use by 5000+ people" in 72 hours.
Comments
Please note that the comment area below has been archived.
thanks a lot
thanks a lot
You all are awesome. Keep
You all are awesome.
Keep working for freedom. You effort is invaluable.
My next donation goes for you.
Keep going!
I love tor, my country
I love tor, my country blocks some site's that i now can open.
keep on the good work ^^
nice work!! and thanks for
nice work!! and thanks for the detailed write up.
great stuff!
great stuff!
Here, in my tor browser the
Here, in my tor browser the google analitics works...!!!!!!
Sometimes, i call a site (whatever which), and i see down in the status bar, "connecting google.analitics..." first, and not prompt direct to the wanted site... GOOGLE SPYING UNDER TOR AS WELL..???!!!!
8-o
How can it be????
They're tracking the exit
They're tracking the exit node, not you. Nothing to worry about.
Same thing, with cia.org
Same thing, with cia.org appearing for a second in the status bar while loading a page...
Realy normal?
Sadly, obfsproxy won't build
Sadly, obfsproxy won't build on RHEL5/CentOS5 systems due to the older version (v2.59, vs. the desired v2.61) of autoconf.
Very nice. I don't live in a
Very nice. I don't live in a particularly censored part of the world, but I imagine everyone will benefit from these changes when governments hatch the idea of expanding data retention laws to make ISPs store more detailed logs about the usage of anonymity networks (and they WILL do it as onion networks become more popular).
Once again, you did
Once again, you did something really, really great. Thanks a lot to all of you!
Outstanding work guys! Keep
Outstanding work guys! Keep on developing such useful tools!
no se mucho de
no se mucho de ejecutamiento del nuevo programa de Obfsproxy pero me gustaria participar en sensurar y estar en el anonimato ya que como se darar cuenta no lo estoy
me gustaria sensurar pero en
me gustaria sensurar pero en anonimato pues todavia no se como
Excellent stuff - this is an
Excellent stuff - this is an awesome answer to the censorship problem.
With BlackBelt Privacy, there is a bundled WASTE client which provides a much easier way to distribute bridge addresses. Although WASTE is not under active development it serves this idea well.
There have been users from China, Iran, Indonesia and other Middle-eastern users on the network.
It also enables people to talk about their Tor experience with other users.
Maybe its not ideal for the Tor community, but some chat room idea could be used for getting bridge addresses into the hands of people that need them ?
Superb work though Tor community !!!
Let's see if you have the
Let's see if you have the BALLS to post this:
Memorable quotes for
Looker (1981)
http://www.imdb.com/title/tt0082677/quotes [imdb.com]
“John Reston: Television can control public opinion more effectively than armies of secret police, because television is entirely voluntary. The American government forces our children to attend school, but nobody forces them to watch T.V. Americans of all ages *submit* to television. Television is the American ideal. Persuasion without coercion. Nobody makes us watch. Who could have predicted that a *free* people would voluntarily spend one fifth of their lives sitting in front of a *box* with pictures? Fifteen years sitting in prison is punishment. But 15 years sitting in front of a television set is entertainment. And the average American now spends more than one and a half years of his life just watching television commercials. Fifty minutes, every day of his life, watching commercials. Now, that’s power. ”
“The United States has it’s own propaganda, but it’s very effective because people don’t realize that it’s propaganda. And it’s subtle, but it’s actually a much stronger propaganda machine than the Nazis had but it’s funded in a different way. With the Nazis it was funded by the government, but in the United States, it’s funded by corporations and corporations they only want things to happen that will make people want to buy stuff. So whatever that is, then that is considered okay and good, but that doesn’t necessarily mean it really serves people’s thinking – it can stupify and make not very good things happen.”
– Crispin Glover: http://www.imdb.com/name/nm0000417/bio [imdb.com]
“We’ll know our disinformation program is complete when everything the American public believes is false.” — William Casey, CIA Director
“It’s only logical to assume that conspiracies are everywhere, because that’s what people do. They conspire. If you can’t get the message, get the man.” — Mel Gibson
[1967] Jim Garrison Interview “In a very real and terrifying sense, our Government is the CIA and the Pentagon, with Congress reduced to a debating society. Of course, you can’t spot this trend to fascism by casually looking around. You can’t look for such familiar signs as the swastika, because they won’t be there. We won’t build Dachaus and Auschwitzes; the clever manipulation of the mass media is creating a concentration camp of the mind that promises to be far more effective in keeping the populace in line. We’re not going to wake up one morning and suddenly find ourselves in gray uniforms goose-stepping off to work. But this isn’t the test. The test is: What happens to the individual who dissents? In Nazi Germany, he was physically destroyed; here, the process is more subtle, but the end results can be the same. I’ve learned enough about the machinations of the CIA in the past year to know that this is no longer the dreamworld America I once believed in. The imperatives of the population explosion, which almost inevitably will lessen our belief in the sanctity of the individual human life, combined with the awesome power of the CIA and the defense establishment, seem destined to seal the fate of the America I knew as a child and bring us into a new Orwellian world where the citizen exists for the state and where raw power justifies any and every immoral act. I’ve always had a kind of knee-jerk trust in my Government’s basic integrity, whatever political blunders it may make. But I’ve come to realize that in Washington, deceiving and manipulating the public are viewed by some as the natural prerogatives of office. Huey Long once said, “Fascism will come to America in the name of anti-fascism.” I’m afraid, based on my own experience, that fascism will come to America in the name of national security.”
I cant write comment from
I cant write comment from tor to sites with facebook-comment option... why?
for example: http://www.hir24.hu/
Great guys and thank
Great guys and thank you.
Now is Feb 20 and Islamic Republic of Iran government blocked all SSL/TLS connections for another time. All VPN and Socks proxies don't work. Only anti-censorship tool available for now in Iran is Obfsproxy.
Keep up great work. We need you.
We are so exciting to
We are so exciting to release this software from you and help you on your way
Good luck
Hey I'm living in Iran,
Hey I'm living in Iran, where can I download it? is it with the regular browser bundle?
https://www.torproject.org/pr
https://www.torproject.org/projects/obfsproxy#download
Yes, it's the regular browser bundle with obfsproxy and some hard-coded bridges.
What are the latest media
What are the latest media activites to report?
Well done and thanks a lot.
Well done and thanks a lot. I have two questions:
1. Will it be available in your debian repositories?
2. Is there a chance to quick replace between obfuscatd and normal mode?
1) Yes, eventually. It's
1) Yes, eventually. It's still way young. You may notice there has not even been a tarball release yet.
2) "Quick replace" does not parse. What do you mean and why would you want this?
good to know names of
good to know names of colonialist CIA coders.
sold dirty rats, how much money you get from CIA?
over 9000
over 9000
hey i'm getting ripped
hey i'm getting ripped off
they are only giving me 8000
Unfortunately, It didn't
Unfortunately, It didn't work now
Hi, Is Tor in a deal with
Hi,
Is Tor in a deal with CIA?
Please, could someone, explain why/how "cia.org " appeared briefly in the Tor window s bottom status bar while a previously (very normal) googled page was loading.
Not very reassuring, if other deals like this would exist...
Thanks
Thanks for tor project
Thanks for tor project
please help of Iran people
please help of Iran people for connect to net
Well if people think Tor is
Well if people think Tor is linking to the CIA and are not themselves working for the CIA, Hence the hate of Tor then all they need to do is load up MS-Fiddler2 and set the gateway as Tor and then point their browser at Fiddler.
What does seem to be missing from Tor is redundancy so that services can be kept running by sharing the service between several users to keep an onion site up and running.
Maybe it can be done by simply sharing the Hostname file between sever machines that replicate the same sites but this is something that will need to be addresses at some stage because too many of the links are dead.
Must go and meet my MOSSAD friends now :)
While I don't believe your
While I don't believe your claim that the Tor browser is actually contacting cia.org, I feel like I should also point out that the US Central Intelligence Agency website is at cia.gov, not cia.org, which is some spam site.
Thanks! Tor connections in
Thanks! Tor connections in China is very difficult. Use Obfsproxy now is very smooth.