Meet Nyx, a Command-Line Tor Relay Monitor

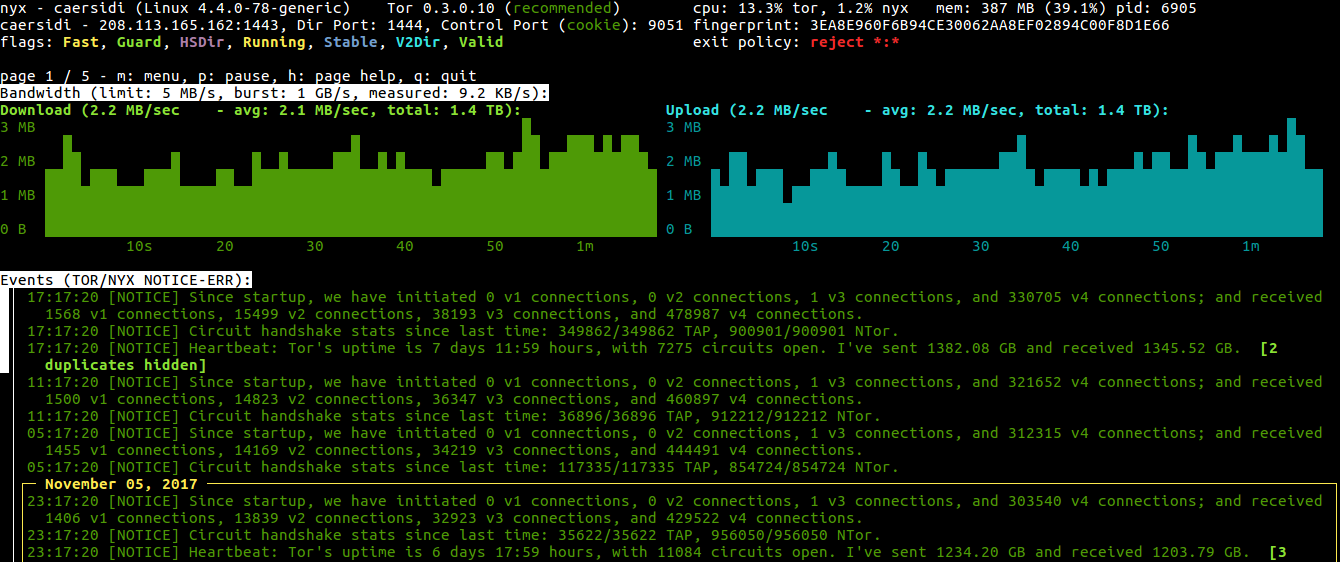
Never let it be said that we don’t give you a choice of ways to interact with Tor data. This month, Damian Johnson, a long-time Tor volunteer, updated a tool that provides real-time information about your relay. Named for the Greek goddess of night, Nyx is a dead-simple tool with data on bandwidth use, connections, logs, and more.
Relay operators can use Nyx to make sure their relay is functioning properly. At a glance, the tool tells them how much bandwidth the relay is using, whether their CPU is constrained, or if something’s wrong and their relay is failing to establish a connection. In keeping with Tor’s commitment to privacy, Nyx scrubs information about user identities and exit connections.
The tool formally known as...
If this all sounds familiar, that’s because this tool used to be called arm. Damian's overhauled the tool, redesigning the tool from the ground up. On his blog, he gives a breakdown of what’s new, including:
- Python 3.x support
- Bandwidth graph now prepopulates when you start up, so you have a graph right away
- Connections are now available without toggling DisableDebuggerAttachment in your torrc
- Support for showing IPv6 connections
Check out the Nyx page to learn more and get the tool.
Comments
Please note that the comment area below has been archived.
On his blog, he gives a…
Hmm... no HTTPS? But Let's Encrypt is free ?
As our noble fellows say …
As our noble fellows say "One SSL certificate a day, keeps the bad guys away..."
insecure connectionhttp:/…
insecure connection
http://blog.atagar.com/nyx-release-2-0/
no https no link !
and what about dns ?
afaik google (and others that i should not name ... ) are not recommended
and what about a contact between relay operator/client ? this tool is like monitoring/reviewing/surveying/analyzing the connection ... so we are un-anonymizing in a way no ?
of course, it is a wonderful tool ... for hackers:testers ... does it help for censoring/shutting down/ remote control ... ?
For specialist only.
Hi m_m…
Hi m_m.
> insecure connection
Yup. As mentioned in my other reply I should get around to this. It's an old blog and I've been busy writing Nyx. :P
> and what about dns ?
> afaik google (and others that i should not name ... ) are not recommended
Sorry, not sure I follow this part. What in particular are your DNS concerns?
> and what about a contact between relay operator/client ? this tool is like monitoring/reviewing/surveying/analyzing the connection ... so we are un-anonymizing in a way no ?
Nope. Nyx scrubs any sensitive information (such as exit and client connections). Information it shows is pretty safe.
> of course, it is a wonderful tool ... for hackers:testers ... does it help for censoring/shutting down/ remote control ... ?
Again, not sure I understand the question. You can use Nyx to reconfigure Tor if that's your question.
> Sorry, not sure I follow…
> Sorry, not sure I follow this part. What in particular are your DNS concerns?
does a relay use dns ? does tor use dns ? does a client use dns ?
dns : relays are using dns _ some are not welcome , it is under the responsibility of the relay operator to pick a 'safe' one _ but how to reject a bad temporary choice as client & as relay operator ; i mean it is not supervised by something or someone else ; all is based on a relay: tor configuration.
Does it exist a command-line option rejecting/blacklisting a 'not recommended dns' or a general hidden/masked supervisor like a table updated every day/hour ?
> Again, not sure I understand the question. You can use Nyx to reconfigure Tor if that's your question.
do you interact using nyx on the quality of the connection ?
do you interfere in the speed, the bottleneck, the choice of the other relays ?
do you control this part (yours as relay operator) in a way that you could redirect the flux or start/stop a tor instance (located at the home client) on demand ?
i understand nix like a sophisticated security tool and like all these similar tools ; it sounds like a big brother feature.
The client or another control layer should be alerted of a ... connection surveyed by nyx because it is done in real time : too many things are based on trust , in this case the relay operator who could be every one every where ... even the worst.
nix could be improved adding an alert/avert when using a bad dns
nix could be improved adding its own setting/running only in preview not in real time.
> does tor use dns ?…
> does tor use dns ?
Don't think so. I can't envision any reasons relays would need DNS. As for clients like Tor Browser it of course makes torrified DNS queries when browsing but this has nothing to do with Nyx.
Nyx is a passive monitoring tool. It shouldn't be possible for anything to leak...
https://nyx.torproject.org/#leaking
thx for your answer , it is…
thx for your answer , it is not an intrusive obscure tool but a passive monitoring (no leak) and it helps a lot the relay operator.
;)
Sorry about that! That's an…
Sorry about that! That's an old personal blog of mine and you're right that it should use Let's Encrypt. Simply haven't gotten around to it yet.
Please check this node…
Please check this node
137.205.124.35
It always send something.
Tor nodes should detect and disconnect abnormal nodes.
no, every one can run a node…
no, every one can run a node : you cannot control the others or you are on the other side , a proprietary tool for controlling the others which the consequences are none security , none anonymity.
a false idea (windows/microsoft usa puerile idea ) runs & runs again : secure = controlled = known = nothing to hide = authorized = clean = citizen = vip = masked/opened = white ? innocent ?
the more you are controlled the less you are in security : that is the real life.
* if you detect something abnormal, you can report it and maybe, it will be shut down after a serious investigation. it should be very suspicious to do that automatically. it can be a leak, a hack a bad operator a misconfiguration a bad update an unknown bug or an electric/cable problem ...
what will be the impact on…
what will be the impact on Tor Network ?
https://www.battleforthenet.com/
What is net neutrality?
Why does it matter?
*startpage alert
It's possible to be used, if…
It's possible to be used, if of any use, by Tor-Browser-Bundle users?
Thank you
Hi. Not entirely sure I grok…
Hi. Not entirely sure I grok the question but yes, Nyx can be used by Tor Browser users to watch the activity of their tor client.
Thank you, you got the…
Thank you, you got the question, I got the answer ;-)
Nyx command show me this:…
Nyx command show me this: Unable to connect to tor. Maybe it's running without a ControlPort?
what should i do? (im newbie)