New OONI & AFTE Report Details The State of Internet Censorship in Egypt

The report uncovers anomalies on Egyptian networks, including censorship and the hijacking of unencrypted HTTP connections for advertising.
- Read the full report in English
- Read the full report in Arabic
- Read the summary of the report in Arabic
Last year, Egypt ordered the blocking of 21 news websites. OONI, a censorship measurement project under the Tor Project, responded by publishing a report on the blocking of (at least) 10 media websites, including Mada Masr and Al Jazeera. In an attempt to identify the remaining blocked sites, Egypt’s Association for Freedom of Thought and Expression (AFTE) ran OONI Probe across multiple networks in Egypt. They subsequently published two research reports, uncovering the blocking of hundreds of URLs (which expand beyond media sites).
OONI and AFTE joined forces. Today, we publish a joint research report on internet censorship in Egypt, based on our analysis of OONI network measurements collected between January 2017 to May 2018.
Our research report is available here. In this post, we share some of the key findings.
Pervasive media censorship
More than 1,000 URLs presented network anomalies throughout the testing period, 178 of which consistently presented a high ratio of HTTP failures, strongly suggesting that they were blocked. Rather than serving block pages (which would have provided a notification of the blocking), Egyptian ISPs appear to primarily block sites through the use of Deep Packet Inspection (DPI) technology that resets connections.
In some cases, instead of RST injection, ISPs drop packets, suggesting a variance in filtering rules. In other cases, ISPs interfere with the SSL encrypted traffic between Cloudflare’s Point-of-Presence in Cairo and the backend servers of sites (psiphon.ca, purevpn.com and ultrasawt.com) hosted outside of Egypt. Latency measurements over the last year and a half also suggest that Egyptian ISPs may have changed their filtering equipment and/or techniques, since the latency-based detection of middleboxes has become more challenging.
The chart below illustrates the types of sites that presented the highest amount of network anomalies and are therefore considered to more likely have been blocked.
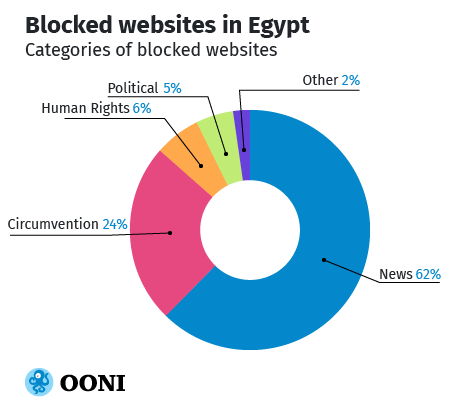
More than 100 URLs that belong to media organizations appear to have been blocked, even though Egyptian authorities only ordered the blocking of 21 news websites last year. These include Egyptian news outlets (such as Mada Masr, Almesryoon, Masr Al Arabia and Daily News Egypt), as well as international media sites (such as Al Jazeera and Huffington Post Arabic). Various Turkish and Iranian news websites were blocked (such as turkpress.co and alalam.ir), suggesting that politics and security concerns may have influenced censorship decisions. In an attempt to circumvent censorship, some Egyptian media organizations set up alternative domains, but (in a few cases) they got blocked as well.
To examine the impact of these censorship events, AFTE interviewed staff members working with some of the Egyptian media organizations whose websites got blocked. They reported that the censorship has had a severe impact on their work. In addition to not being able to publish and losing part of their audience, the censorship has also had a financial impact on their operations and deterred sources from reaching out to their journalists. A number of Egyptian media organizations have suspended their work entirely, as a result of persisting internet censorship.
Many other websites, beyond media, appear to have been blocked as well. These include human rights websites (such as Human Rights Watch, Reporters without Borders, the Arabic Network for Human Rights Information, the Egyptian Commission for Rights and Freedoms, and the Journalists Observatory against Torture) and sites expressing political criticism (such as the April 6 Youth Movement), raising the question of whether censorship decisions were politically motivated.
“Defense in depth” tactics for network filtering
Security experts are probably familiar with the “defense in depth” concept in which multiple layers of security controls (defense) are placed throughout an IT system, providing redundancy in the event that a security control fails. In Egypt, ISPs seem to apply “defense in depth” tactics for network filtering by creating multiple layers of censorship that make circumvention harder.
This is particularly evident when looking at the blocking of Egypt’s Freedom and Justice Party (FJP) site. Our testing shows that different versions of this site (http://www.fj-p.com and http://fj-p.com) were blocked by two different middleboxes. In doing so, Egyptian ISPs added extra layers of censorship, ensuring that circumvention requires extra effort.
Not only were numerous circumvention tool sites (including torproject.org and psiphon.ca) blocked, but access to the Tor network appears to be blocked as well. Measurements collected from Link Egypt (AS24863) and Telecom Egypt (AS8452) suggest that the Tor network is inaccessible, since the tests weren’t able to bootstrap connections to the Tor network within 300 seconds. In recent months, more than 460 measurements show connections to the Tor network failing consistently. Similarly, measurements collected from Etisalat Misr (AS36992), Mobinil (AS37069) and Vodafone (AS36935) indicate that access to the Tor network is blocked. The Tor bootstrap process is likely being disrupted via the blocking of requests to directory authorities.
“Defense in depth” tactics also seem to be applied in relation to the blocking of Tor bridges, which enable Tor censorship circumvention. Vodafone appears to be blocking obfs4 (shipped as part of Tor Browser), since all attempted connections were unsuccessful (though it remains unclear if private bridges work). All measurements collected from Telecom Egypt show that obfs4 works. Given that bridges.torproject.org is blocked, users can alternatively get Tor bridges by sending an email to bridges@torproject.org (from a Riseup, Gmail, or Yahoo account).
Ad campaign
Back in 2016, OONI uncovered that state-owned Telecom Egypt was using DPI (or similar networking equipment) to hijack users’ unencrypted HTTP connections and inject redirects to revenue-generating content, such as affiliate ads. The Citizen Lab expanded upon this research, identifying the use of Sandvine PacketLogic devices and redirects being injected by (at least) 17 Egyptian ISPs.
Over the last year, hundreds of OONI Probe network measurements (collected from multiple ASNs) show the hijacking of unencrypted HTTP connections and the injection of redirects to affiliate ads and cryptocurrency mining scripts. A wide range of different types of URLs were affected, including the sites of the Palestinian Prisoner Society and the Women’s Initiatives for Gender Justice, as well as LGBTQI, VPN and Israeli sites. Even the sites of the United Nations, such as un.org and ohchr.org, were among those affected by redirects to ads.
Expand upon our research
This study is part of an ongoing effort to monitor internet censorship in Egypt and around the world. Since this research was carried out through the use of free and open source software, open methodologies and open data, it can be reproduced and expanded upon.
Anyone can run OONI Probe on Android, iOS, macOS, Linux, and on Raspberry Pis. Tens of thousands of OONI Probe users from more than 200 countries do so every month. Thanks to their testing, millions of network measurements have been published, shedding light on information controls worldwide.
But censorship findings are only as interesting as the types of sites and services that are tested. We therefore encourage you to contribute to the review and creation of test lists, to help advance future research in Egypt and beyond.
To learn more about this study, read the full report here.
Comments
Please note that the comment area below has been archived.
This is all due to Egyptians…
This is all due to Egyptians foolishly overthrowing their first democratically elected president for a military regime by the most incapable ruler in its history: al-Sisi
Ta7ya Misr ya as7ab Tor!
The most weak place in Tor…
The most weak place in Tor is bootstrap. I.e., how to get private bridges. If, for example, Tor client send specific broadcast and, then, all nearest private obfuscated bridges reply "We're here, you're welcome!" - like DHCP does, for example - this scheme will more simple for end-users and more reliable. To protect from probing, Tor, for example, can use some specific crypto schemes for auth on bridges. Just an idea.
Does that help? *user…
Does that help?
*user broadcast* "let me join tor"
*censor* "no"
Or the censor may send their own broadcast and block all responding bridges.
The Internet doesn't have any broadcast feature, unless you include nmap/massscan. Very noisy tools. Censorship resistance usually needs to be quiet!
The tor developers are actively researching alternatives. Hyphae is promising.
https://patternsinthevoid.net/hyphae/hyphae.pdf
shouldn't the egyptian in…
shouldn't the egyptian in this illustration be wearing a ballcap or something because we can't see the face but the features of the head piece are obvious it's an egyptian!