#MoreOnionsPorfavor: Onionize your website and take back the internet
Starting today, July 8th, the Tor Project is running a one month campaign called #MoreOnionsPorfavor to raise awareness about onion sites, that is, websites available over onion services. We recently released a feature called Onion-Location in Tor Browser that announces to users if a website has an onion site available. Join us to make a more secure web! To participate, enable Onion-Location, share your onion site using the hashtag #MoreOnionsPorFavor on your favorite social media, and we'll select some onion service operators to receive a Tor swag. See below for all the details.
As protests are sparkling around the world, we know that the struggles for a more just society are closely surveilled by those in power. The things that we do online, where we are, the websites that we've visited, who we've talked to data being collected and analyzed to draw the social graph of activists and monitor. As many digital security trainers point out: protests may have an end, but metadata forever.
he Tor Project we develop privacy enhancing technologies to protect and advance human rights. is called Onion Services. way to protect users metadata like their real location, end-to-end authentication and end-to-end encryption by default when visit a website. One can easily spot an onion service as the domains are a public key encoded as an address ending with .onion.
Since users have a legit and increasing concern safe online, developers, system administrators and websites owners can and should offer a more secure experience to users. If you run a website, you can improve its security by offering a version of your site over onion services.
Recently we implemented a way to announce and publicize onion site using Onion-Location. When visi a website that has both onion services and Onion-Location enabled, Tor Browser will display an information pill telling that there's a more secure version of the website ,and will be asked to opt-in to upgrade to the onion service on their first use.
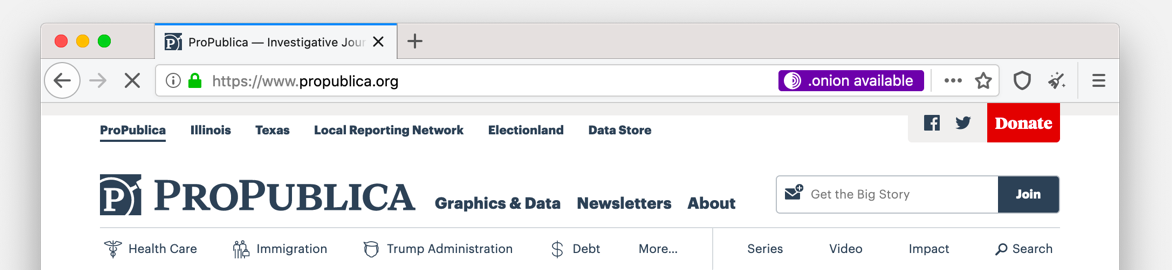
Many web administrators already joined us and made their websites available over onion services and Onion-Location. For example, ProPublica, DEF CON, Privacy International, Riseup.net, Systemli.org, Write.as. And now, we invite you to join this campaign: #MoreOnionsPorfavor.
Setting up an onion site with Onion-Location
Some onions are very easy to cultivate, but others you may need professional support. For enterprise scale websites, we recommend getting in touch with us.
First, you need to configure your web server so it doesn't give away any information about your user location. As any other service connected to the internet, it can be risky if it's misconfigured. Therefore, we recommend reading and following onion services documentation and best practices.
After you've configured your web server and onion service, you can setup Onion-Location.. It's worth mention that Onion-Location will only work if you've already setup an TLS certificate for your domain, i.e. Let's Encrypt.
Once you've set up your onion site, send an email to <@torproject.org> and announce it on your favorite social media using the hashtag #MoreOnionsPorfavor. Next month, we will select some onion site operators to receive a Tor swag as a token of our gratitude for your help defending the secure internet. Set up your onion site and email us by to qualify.
Other ways to help
If you can't run an onion service but want to help to take back the internet, there are other ways you can help:
- Make a donation to the Tor Project to support our work developing and sharing tools for privacy and freedom online.
- Help translate Tor Community portaland documentation including information on how to set up an onion service.
- Ask to your favorite website to make th available over onion services.
It's time to raise the bar of privacy and onionize your site!
Comments
Please note that the comment area below has been archived.
Before you ask about blog…
Before you ask about blog.tpo Onion-Location: we want to move this blog to a new platform, so we will have Onion-Location at some point this year, but not now.
**Thumbs Up**
**Thumbs Up**
Good news, good news.
Good news, good news.
It's worth mention that…
typo? e.g. Let's Encrypt
Ha. Yes, your domain that…
Ha. Yes, your domain that serves the Onion-Location header can have an https cert from any CA -- it doesn't have to be only Let's Encrypt.
But that said, I admit that I like the subtle implication that Let's Encrypt is the future of certificate authorities, rather than the historical for-pay proprietary CA mafia, and that in the future we should consider "CA" and "Let's Encrypt" as synonyms. :)
Can you say monopoly?
Can you say monopoly?
And the other typo is that…
And the other typo is that it should be "a TLS cert", not "an".
Also, "setup" should be "set…
Also, "setup" should be "set up", as this instance is functioning as a verb, and not an adjective or noun.
Yay ! Let's create a safer…
Yay ! Let's create a safer internets !
Also, should this Onion-Location header be displayed for every client, or only if the servers "detects" it's a Tor exit node ?
We have a ticket for this…
We have a ticket for this discussion:
https://gitlab.torproject.org/tpo/applications/tor-browser/-/issues/322…
Feel free to request your account on the sign-in page.
You're right: large websites…
You're right: large websites might not want to spend the extra bandwidth of writing an Onion-Location header in every page they serve, on the tiny chance that the reader happens to be a Tor Browser that knows about the header.
Facebook definitely counts as large, and I expect some others might consider themselves in this category of "too large to spend bandwidth on that".
There are really two pieces to this story, and Onion-Location is only one piece. The second piece is, as you say, that large websites will need to use some mechanism for deciding whether to include the Onion-Location header.
One option is proposed on the ticket that Gus pointed to, which is a great place for further discussion:
https://gitlab.torproject.org/tpo/applications/tor-browser/-/issues/322…
The idea there is that we advertise our onion capability in the browser's User-A
gent header, so websites aren't left to guess.
In the mean time, the best approach for making that decision right now is to use something like the 'bulk exit list' exporter:
https://lists.torproject.org/pipermail/tor-project/2020-March/002759.ht…
I'll note that if the goal is to avoid spending too much extra bandwidth, and if we're using the Onion-Location header, the "is it a Tor user" detection doesn't have to be perfect. Whereas a different mechanism, like "detect if it's a Tor user and then give them a 302 redirect", has much less room for error.
Also, for smaller websites, serving the header to every user is easy to do and has little downside.
Would all of the other…
Would all of the other Torified apps on the network (that are not Tor Browser) have to also edit their UA strings or listen for Onion-Location to be redirected? Many don't have the UA even exposed for editing and merely offer general proxy settings.
@Tails users: for some…
@Tails users: for some reason it seems that the Tor Browser 9.5.1 which comes with Tails 4.8 is not yet configured to "always prioritize onions".
In the tool bar, look in Preferences -> Privacy and Security and choose "always prioritize onions". For the duration of that Tails session (and beyond if you use a Tails USB configured to remember settings, which might be a bit dangerous), you will be automatically connected to the onion mirror for those sites you visit which have onions. I just tested this and it works for the document cited in the post:
http://vww6ybal4bd7szmgncyruucpgfkqahzddi37ktceo3ah7ngmcopnpyyd.onion/e…
Very impressive, BTW. I hope people who already know how to set up a clearnet website will find it very easy to follow.
About 2-3 years ago, Tails Project was working on a big project called "Tails server", which I think would have basically been a carefully preconfigured onion site you could set up "out of the box" (with minimal site-specific configuration such generating a unique onion keypair). I have the impression they had to give up on that as too challenging for the next few years. Do you now more?
Done! Thank you for this…
Done! Thank you for this great new feature.
This post tries to convince…
This post tries to convince web admins to set up onions but makes no mention of EOTK, the tool I've seen mainstream outlets talk about the most when it comes to setting up onions. The onion services documentation mentions it in passing at the very bottom.
Dear anonymous, indeed, EOTK…
Dear anonymous, indeed, EOTK is a great tool!
If you want to help improve the documentation of Tor community, we have a ticket on that:
https://gitlab.torproject.org/tpo/web/community/-/issues/136
Maybe you could start drafting and then others could engage?
Thanks!
The point is that the post…
The point is that the post wants to appeal to newbies, and newbies prefer EOTK because it makes setup easier, but the post doesn't mention EOTK, so the way the post is written as of this reply, it won't be as appealing as it hopes to be.
Why does DuckDuckGo's…
Why does DuckDuckGo's website not have this feature?
Maybe they haven't been made…
Maybe they haven't been made aware of it yet? And Tor Browser should use the .onion version by default anyway.
Is it #MoreOnionsPorfavor…
Is it #MoreOnionsPorfavor with a lowercase f as appears most times in this blog post or #MoreOnionsPorFavor with a capital F that appears once in this post, but fits the camel case styling better?
You can use both. :-)
You can use both. :-)
Absolutely impressed. Thank…
Absolutely impressed. Thank You! Great project at a time like this.
Is there a reason why the…
Is there a reason why the Onion-Location header has to specify the full URL? I would have guessed that almost all websites have the same path string for their onion and regular domains.
Wouldn't it make sense to alternatively define a short format to allow operators to define the Onion-Location header with just the domain name (no protocol, port or path) for cases where no special port or different URL is required? This would also be one way to save on bandwidth, which seems to be one of the concerns with this header.