OONI Bridge reachability study and hackfest

Has a Tor bridge already been blocked in a given country? Being able to answer that question would allow Tor to provide more efficient circumvention methods to those who need them. OONI, the Open Observatory of Network Interference is now actively collecting data on bridge reachability. We are also interested in having a better understanding of how reactive censors are in blocking new bridges distributed via Tor Browser and how effective they are at inhibiting usage of particular pluggable transport.
The countries we are focusing on in this survey are China, Iran, Russia and Ukraine. We call these our test vantage points.
From every test vantage point we perform two types of measurements:
- A Bridge reachability measurement that attempts to build a Tor circuit using the bridge in question.
- A TCP connect measurement that simply does a TCP connect to the bridge IP and port.
To establish a baseline to eliminate the cases in which the bridge is marked as blocked, while it is in fact just offline, we measure also from a vantage point located in the Netherlands.
So far we have collected about a month worth of data and it is as always publicly available for download by anybody interested in looking at it.
To advance this study at the end of October we did a OONI hackfest in Berlin. Helped by the ubiquitous sticky notes we were able to come up with a plan for those days of work and for continuing the project.
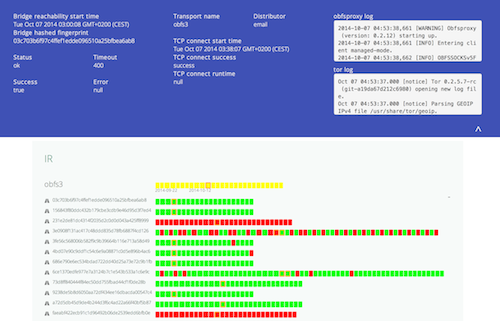
The first visualisation we produced is that of the reachability of bridges categorised by country and pluggable transport over time. This simple visualisation already conveys a lot of information and has proven itself a useful tool also in debugging issues with ooniprobe and the tools we use.
You can visit the actual page by clicking on the picture above.
Please note that because the tests are new and experimental you might find inaccuracies or bugs, so don't seriously rely on it for research just yet.
We also developed a data pipeline that places all of the collected OONI reports into a database. This makes it much easier to search/aggregate and visualise the data of the reports.
To read more about this project check out the ooni-dev mailing list thread on this topic.
This project is still in it's very early stages of development, but we would love to hear feedback on it or your cool visualization ideas, as well as any questions regarding Tor bridge reachability (or more in general on Internet censorship) that you would like us to answer!
Comments
Please note that the comment area below has been archived.
From the picture it looks
From the picture it looks like a nice site. When I go there it requires javascript which I don't enable for most sites. It's a shame it doesn't have a dumbed down non-javascript version for us with tinfoil hats
All of the data used for
All of the data used for producing the visualisations is public, it would be great if you could make a non javascript version of the graphs with it!
The javascript code used to create it is in this repository: https://github.com/Shidash/OONI-Bridge-Reachability-Timeline
大家好!meek-amazon还是
大家好!meek-amazon还是挺不错的!
Is it possible to run
Is it possible to run Bridges on IPv6 ?
So it might be possible to set up bridges wich can change their ip Adress every day to a new one. making it very ineffiecient to block it. Or setting up one ipv6 Bridge for every user who wants to use TOR.
combined with SSL VPN it should be hard for any gov organization to track down these bridges.
If the bridge's IPv6 address
If the bridge's IPv6 address changes daily, how does a client know at which address the bridge is located (and thus should connect)?
In india, some ISP's
In india, some ISP's blocking tor. Since last 3 days I 'm trying to access tor from Windows8.1 /10 and Tails, I 'm not able to connect Tor network. I got the below error message. Also not able to download the unstable version of the Tor for windows.
Please guide me
Good people are good thinkers. When such type of good thinkers mate & present their dreams in the form of reality, it came in the form of Tor. Best of luck Tor team for there great job.
Best Regards
White Panther.
You can using meek.
You can using meek.