New Release: Tails 6.15

Tails 6.15 is out.

Tails 6.15 is out.

Tor Browser 14.5.1 is now available from the Tor Browser download page and also from our distribution directory.
Opting out of Big Tech means investing in better alternatives. That's where Tor, Tor Browser, and Tails come in. Help fuel the development of truly private tools.
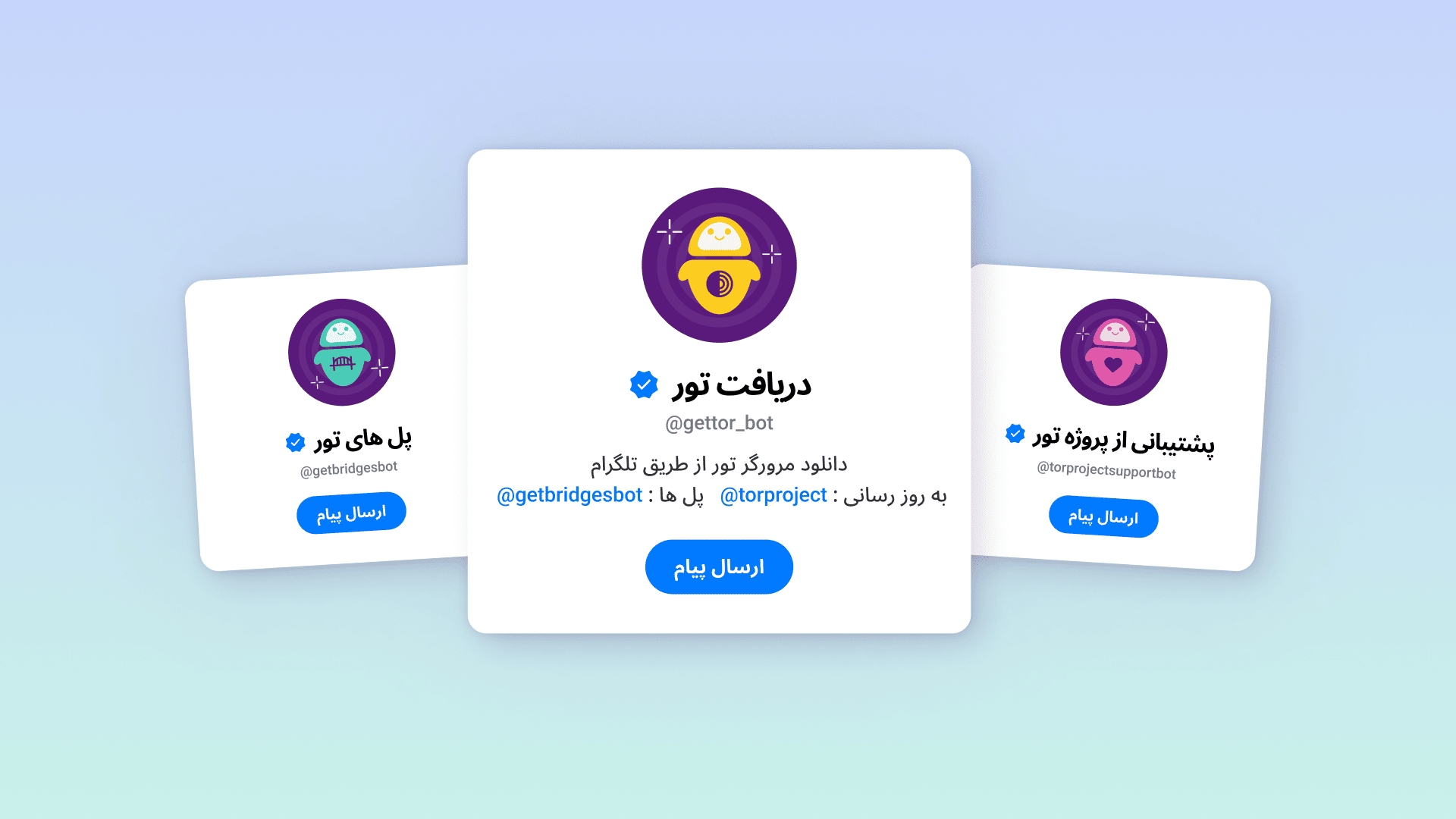
Farsi-speaking users can now get direct support from the Tor Project! If you need help connecting to the Tor network, our team is available to assist you.

Tor Browser 14.5 is now available, introducing Connection Assist to Android for the first time, and including the Belarusian, Bulgarian and Portuguese (Portugal) languages for all platforms.

This release is an emergency release to fix security vulnerabilities in the Linux kernel and the implementation of the Perl programming language.

Tor Browser 14.5a6 is now available from the Tor Browser download page and also from our distribution directory.

Today, we are releasing 6.14.1 instead of 6.14 because we discovered an important issue while testing 6.14 on Tuesday and had to start the release process again to fix it.
Arti 1.4.2 is released and ready for download.

Tor Browser 14.0.9 is now available from the Tor Browser download page and also from our distribution directory.